Charlie and the Chocolate Heist

We were looking for a way to convey the breadth and depth of the different types of roles that exist in cybersecurity, that was fun and engaging. Introducing: The Chocolate Heist!
Last year, we were asked to give an awareness presentation to a group of girls aged 9-11 years old about the different roles in cybersecurity. To make the presentation more interactive, we decided rather than just telling them about all of the roles they could possibly do in the industry, we would actually get them to role play some of them in a workshop (and sneakily hopefully learning something along the way).
We used a range of AI generators to create imagery and videos following scripts that we wrote that covered a particular story arc, using some of the tools detailed on this previous post.
The Story
The focus of the story centred around corporate espionage and something that all kids love - chocolate! But it had to have a twist - not the “Please sir can I have some more?” variety - something with more drama. So what if something happened to the supply, or secret ingredients were tampered with, warehoused stock was stolen, or upcoming recipes were nabbed for financial gain? Introducing:
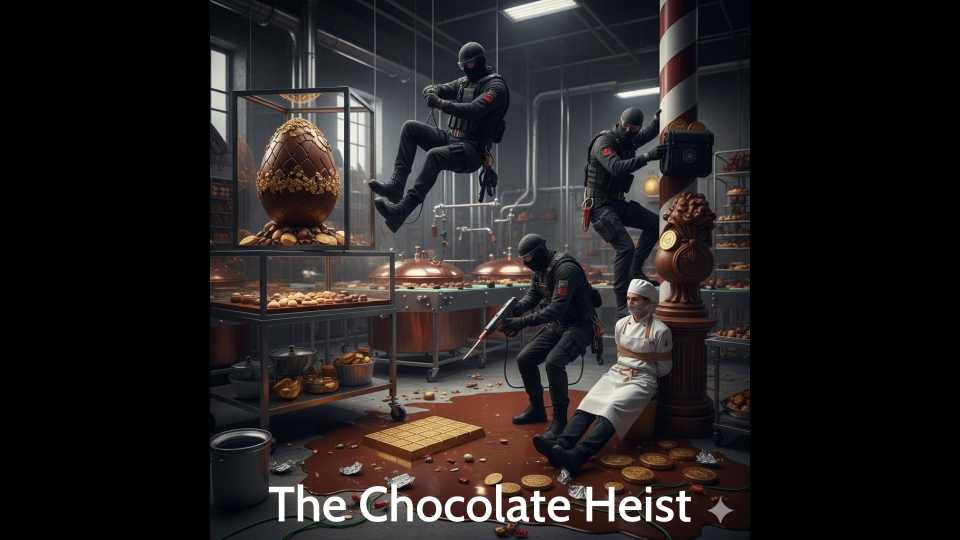
We used the great Charlie and the Chocolate Factory as the base of our story, with the narrative around an upcoming birthday of the factory and the company re-releasing five golden tickets as Olivia (an employee at the factory) talks us through:
Task 1
The golden tickets will be included in chocolates that lucky finders will have to find to “win a year’s supply of chocolate” (similar to the story), however there is a problem. The company realised that just like in the past, some malicious people might try and create fake golden tickets:
The first task was to figure out how they could identify the correct winners, from those creating their own fake tickets.
For this, example tickets were created as per below so that each team had actual phyiscal tickets to discuss how they could verify legitimate ticket holders (i.e. those with the correct authentication details) to be allowed into the factory.

You can download the template word document that we used here to modify for your own purposes, with gold paper acquired from your local stationery shop.
The exercise led towards thinking about multiple factors of authentication (i.e. MFA) and enabling the lucky finders to know something (a secret under the wrapper), as well as have something (the golden ticket):
Task 2
We then got contacted by Anna in their IT team, as due to the amount of media attention for the advertising campaign, they were receiving a lot of website traffic that was causing problems:
The second task was to figure out how the teams could protect the systems and reduce the flow of malicious traffic coming to the website.
For this, we provided literal small chunks of physical garden hose, as well as some hose guns/nozzles to discuss how these props could help stop or slow the malicious traffic.
The exercise led towards thinking about restricting the unwanted traffic through rate limiting, or filtering it out i.e. through things like Distributed Denial of Services (DDoS) controls or even Web Application Firewalls (WAFs).
Task 3
Anna commended us on our choice of rate limiting as a solution to reduce the malicious traffic, but during the call something weird happened:
Oh no! Willy Wonka’s Chocolate Factory has been infected with ransomware!
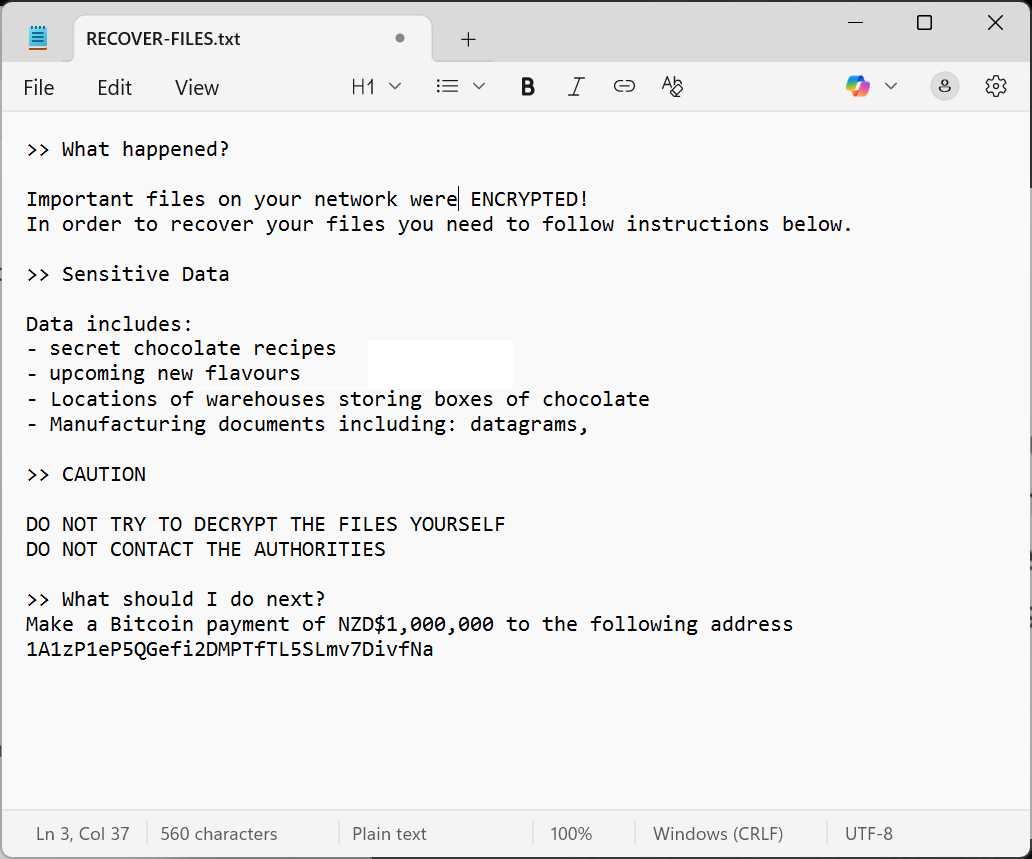
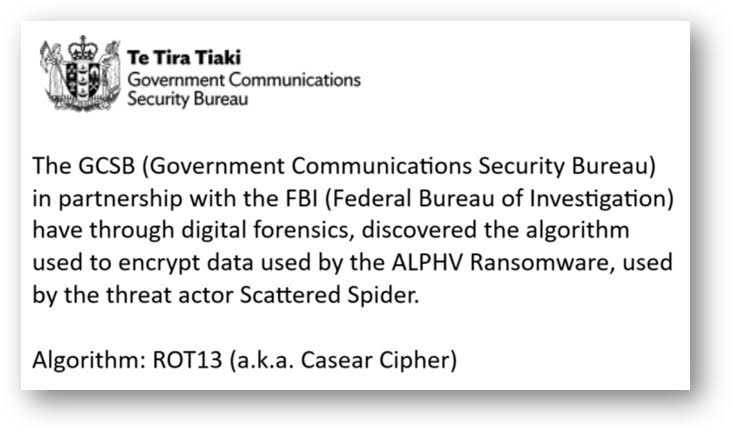
Luckily for us, the Government Communications Security Bureau (GCSB) have found that the encryption cipher being used is ROT13 a.k.a. a Caesar Cipher.
For this, each team was provided with part of the encryption key to decrypt and a hint to solve it.
Conclusion
Once each team had managed to decrypt their part of the encryption key, when they joined each part together, they were able to recover all of the company’s data and get chocolate flowing again - phew! The encryption key also gave the clue to who had targeted Wonka’s Chocolate Factory in the first place…
As a thank you, the CEO Jane called them directly to tell them they’d be getting free chocolate for being great cybersecurity professionals. We then handed out chocolate for everyone to enjoy for a job well done - yum!
Resources
If you’d like to run your own security awareness workshop, feel free to use the videos above and the materials below.
- The Chocolate Heist Powerpoint Presentation - 88Mb
- Task 1 - Golden Ticket Template Word Document - 530Kb
- Task 3 - ROT13 / Caeser Cipher - Encryption Key Challenge - 800Kb
We’d appreciate if you do use the materials, to tag us in your LinkedIn post and let us know how you get on! :)
Or if you’d like us to run a security awareness training workshop for your organisation, then please get in touch.